XM Cyber
Context-driven exposure insights across your entire attack surface, to know what to fix first
Simulate, Remediate — Strengthen Your Security with XM Cyber
Traditional security tools often focus on isolated vulnerabilities, leaving organizations blind to how attackers actually exploit them. XM Cyber changes this approach by providing a continuous exposure management platform that simulates real-world attack scenarios to uncover hidden attack paths.
By taking an attacker’s perspective, XM Cyber enables organizations to identify and prioritize the most critical risks before they can be exploited.
XM Cyber is a continuous exposure management platform that identifies and mitigates attack paths before attackers can exploit them.
Key Features and Capabilities:
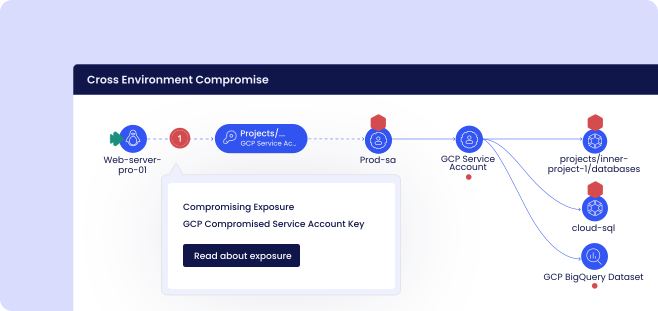
Attack Path Simulation
Map and analyze potential attack paths across your environment.
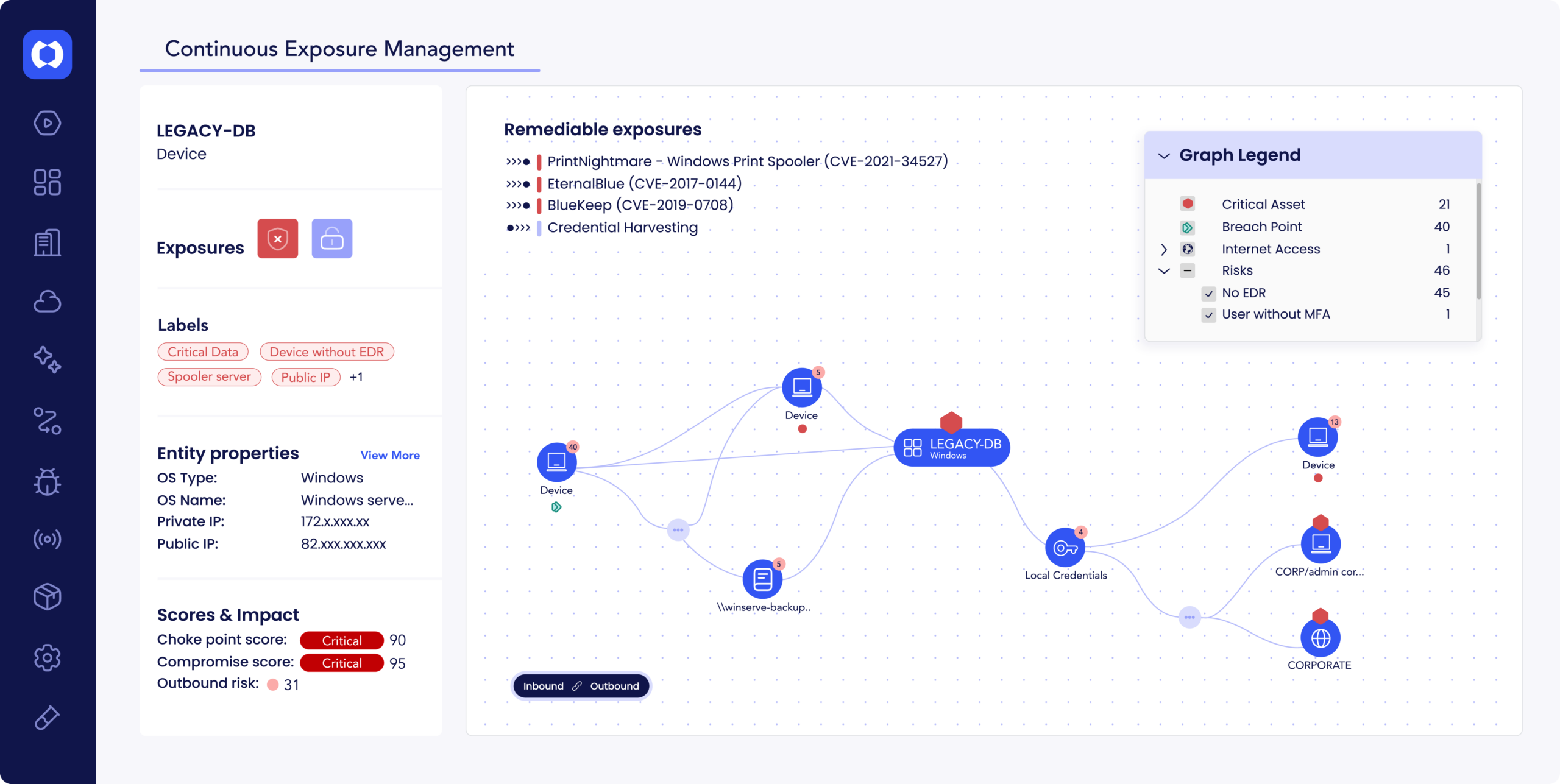
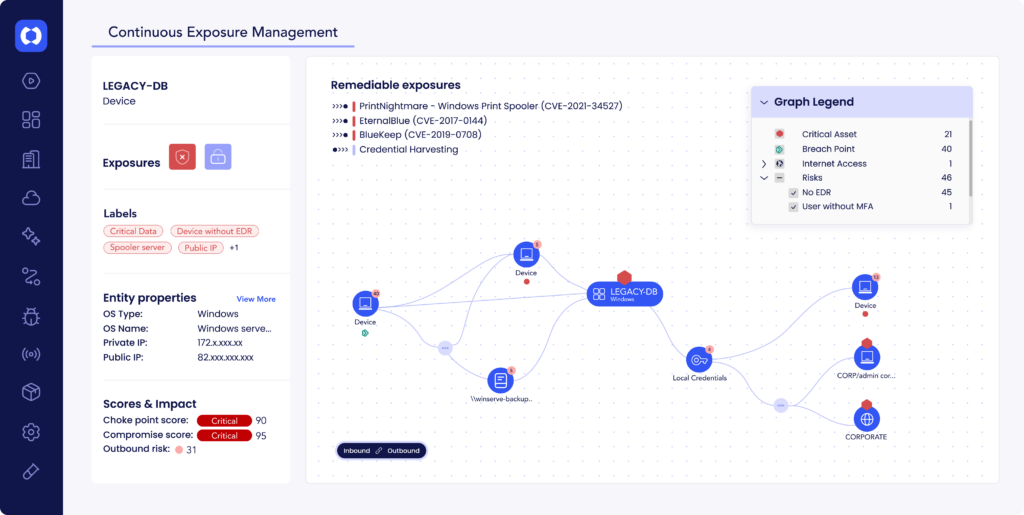
Continuous Exposure Management
Continuously assess and monitor security posture.
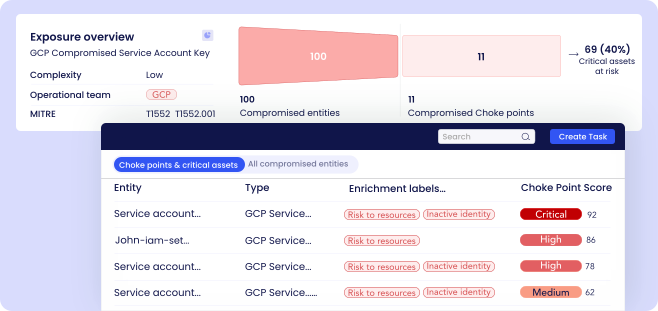
Risk Prioritization
Focus on vulnerabilities that pose the greatest real-world risk.
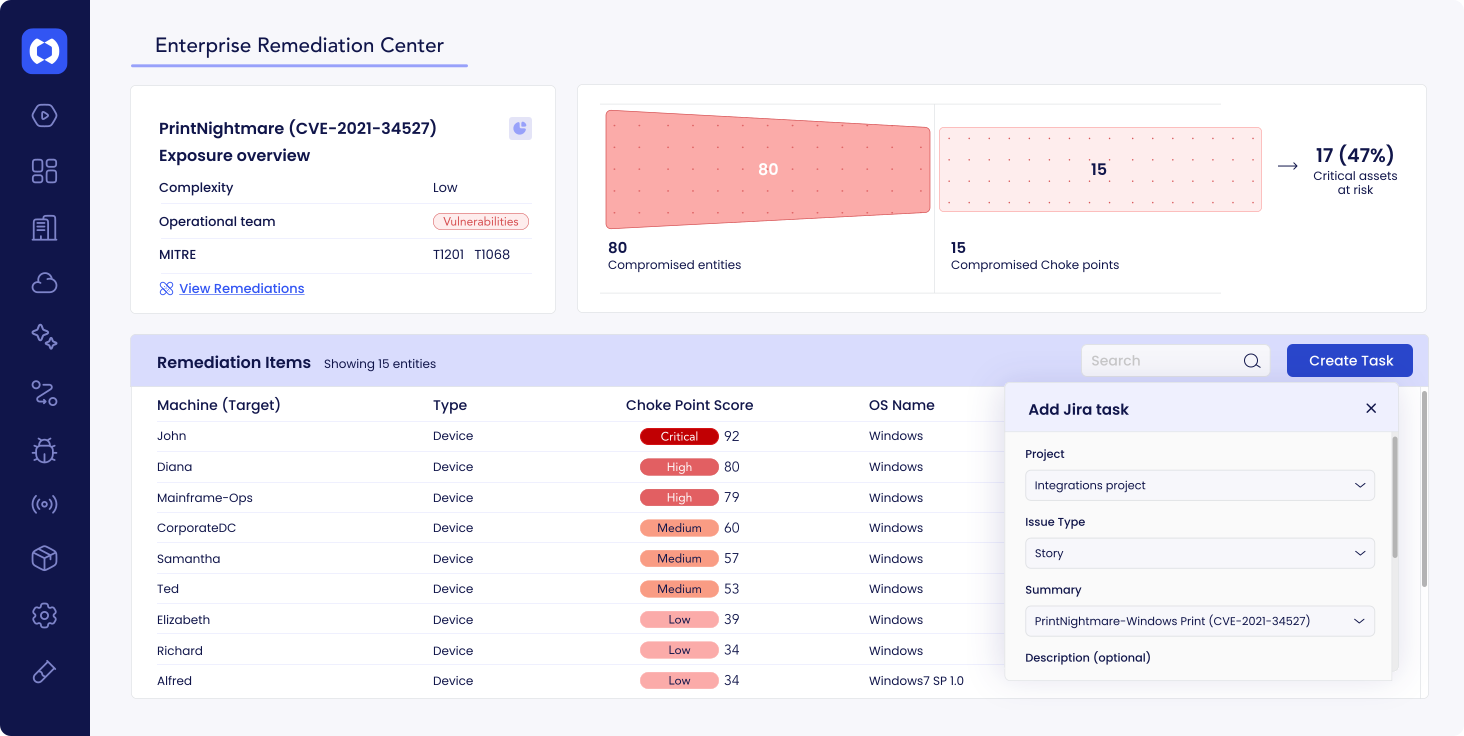
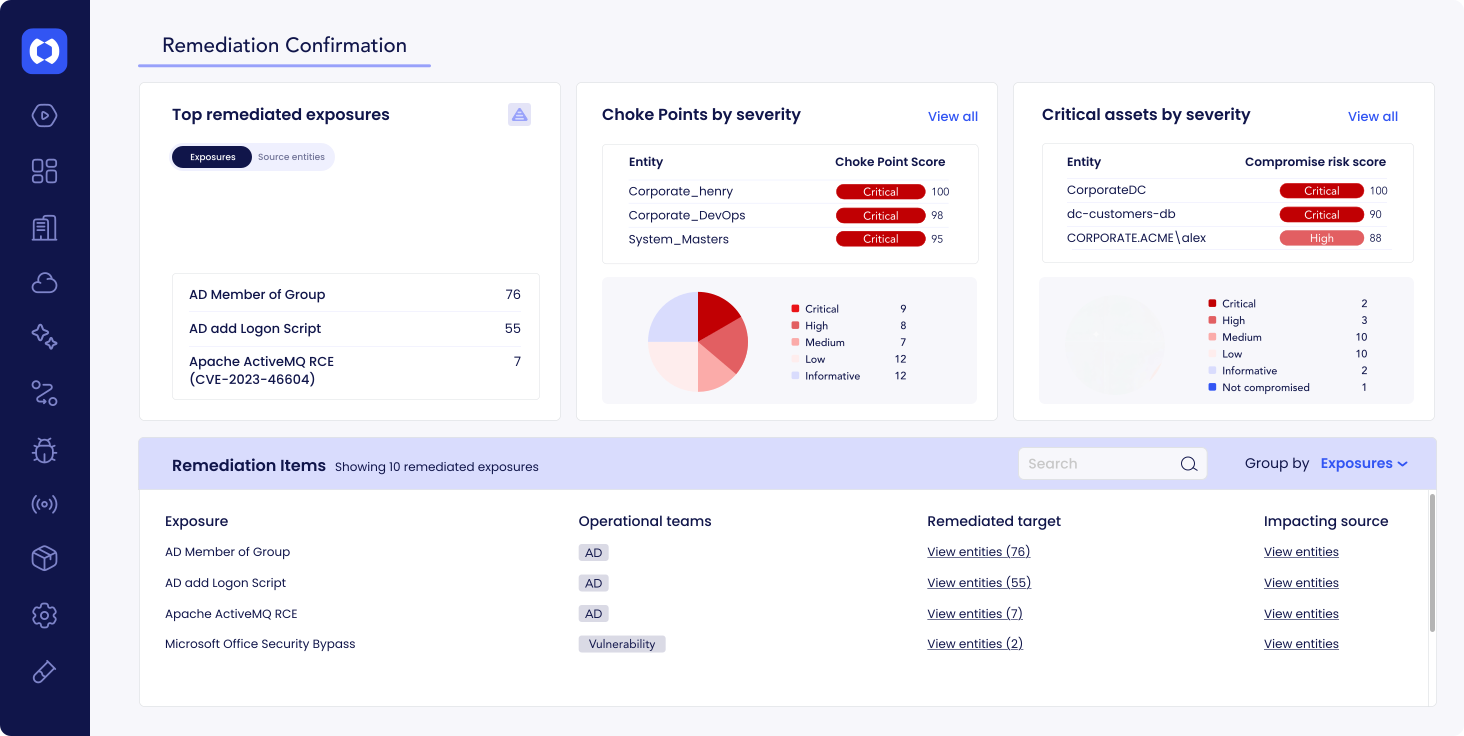
Remediation Guidance
Receive clear, actionable steps to eliminate risks.
Continuous Monitoring
Detect changes in your environment and reassess risk automatically.
Integration with Security Tools
Enhance existing security investments with deeper insights.
Strength
- Unique attacker-perspective analysis
- Proactive risk identification
- Clear visualization of attack paths
- Actionable remediation insights
- Continuous monitoring capabilities
Use Cases
- Exposure Management: Identify and reduce risk proactively
- Security Posture Improvement: Strengthen defenses
- Red Team Simulation: Understand attack scenarios
- Risk Prioritization: Focus on high-impact vulnerabilities
XM Cyber helps organizations move beyond reactive security by showing how vulnerabilities can be chained together in real attack scenarios—providing a more realistic view of risk. XM Cyber empowers organizations to eliminate critical attack paths and adopt a proactive, attacker-focused approach to cybersecurity.
See All Exposures, Fix What’s Critical
XM Cyber’s Continuous Exposure Management Platform cuts through the endless lists, providing graph-based context to prioritize the exposures that put your critical business assets at risk.
Gain a unified view of your entire attack surface, revealing how diverse exposures interconnect to create attack paths. With risk-based context to the business, you can identify and fix the exposures with the highest remediation ROI to optimize security posture and improve resource efficiency.
Get in Touch
If you have any questions or need assistance, we’re here to help.
Headquarter
+65 6513 0018
Email Address
sales@ace-pac.com
Ready to enhance your cybersecurity strategy?
Transform your organization’s cybersecurity approach into a competitive edge. Schedule a consultation with us today to explore tailored solutions that meet your needs. Don’t wait—empower your security posture now.
Products
About Us
Resources
Receive Our Newsletter
© 2026 ACE PACIFIC GROUP