Black Kite 2026 Third-Party Cyber Risk Report Explained
In 2025, 136 verified third-party cyber incidents impacted 719 named organizations, while an estimated 26,000 additional companies were silently affected.
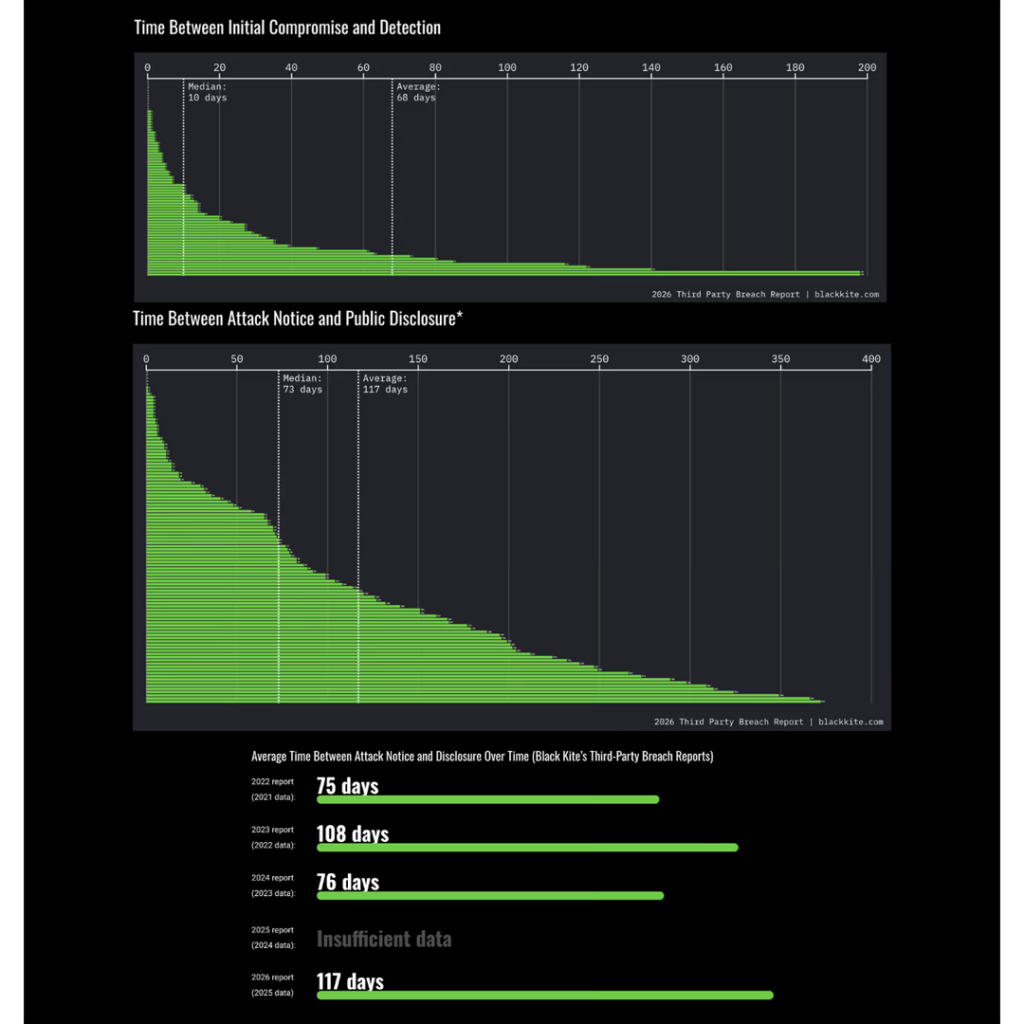
Disclosure delays worsened significantly—from 76 days to 117 days (average).
This report delivers a clear message:
Traditional third-party risk management is no longer effective—and CISOs must act now.
2025 by the Numbers: The Iceberg Beneath the Surface
- 136 verified third-party cyber incidents
- 719 publicly named victim organizations
- Each vendor impacted an average of 5.28 downstream companies
- ~26,000 “shadow victims” (unidentified affected organizations)
- 433 million individuals impacted — equivalent to the population of the EU
- Disclosure delay:
- Median: 73 days
- Average: 117 days
These figures point to a structural shift:
The speed of impact now far exceeds the speed of disclosure.
2025 was not just “another bad year”— it marked a fundamental transformation in supply chain cyber risk.

The Shadow Victim Layer: You May Already Be Affected
The most alarming insight is not what made headlines—but what didn’t.
In 27 incidents, vendors disclosed impacts only in aggregate (“~X organizations affected”) without naming victims.
This creates a dangerous reality:
- Your data may already be circulating on the dark web—without your knowledge
- You cannot initiate incident response because you don’t know you’re compromised
- Regulatory obligations may already be triggered without action
CISO Alert:
In 72.8% of verified incidents, the threat actor remains unknown or undisclosed.
You don’t know:
- if you were affected
- who attacked your vendor
- what techniques were used
Any defense strategy based on “knowing the attacker” becomes ineffective.
The 73-Day Silent Window: Attackers’ Golden Opportunity
Even when vendors detect breaches, they rarely notify immediately. Disclosure delays are worsening:
In cybersecurity terms, 73 days is not investigation time—it’s operational time for attackers.
During this window, attackers can:
- Fully map networks and establish persistence
- Exfiltrate entire databases (PII, IP, supply chain links)
- Compromise credential ecosystems and impersonate vendors
- Extend attacks downstream via trusted relationships
Extreme cases highlight systemic failure:
- APT detection delays: up to 730 days
- Unauthorized access: 662 days
- Malware presence: 628 days
These are not anomalies—they are patterns.

Concentration Risk: Your Most Critical Vendors Are the Most Fragile
Analysis of the Top 50 shared vendors in the Forbes Global 2000 ecosystem reveals a counterintuitive truth:
The more critical the vendor, the higher the risk.
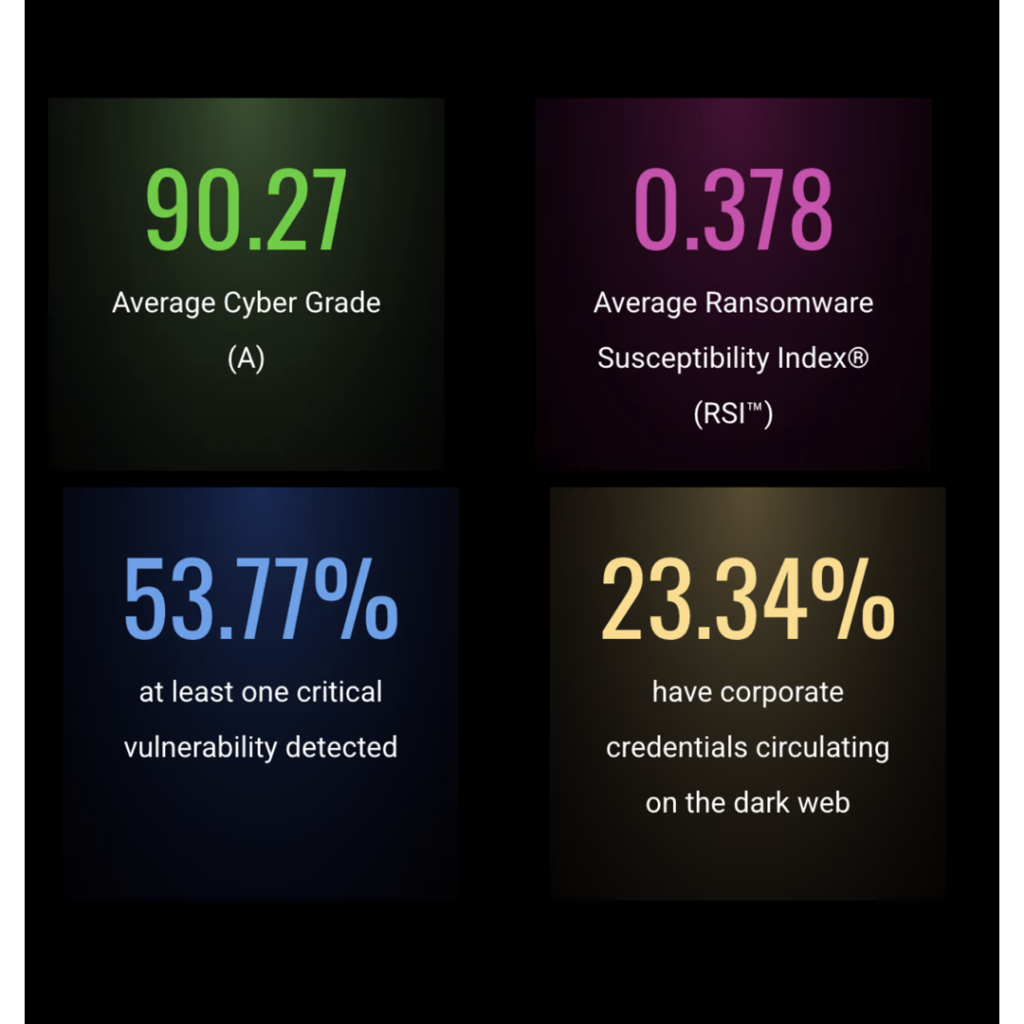
Key Risk Indicators (KRI)
- 70% have vulnerabilities listed in CISA KEV
- 84% have critical vulnerabilities (CVSS ≥ 8)
- 62% exposed credentials in infostealer logs
- 30% leaked credentials within the past 90 days
- 80% exposed phishing URLs
- 40% actively targeted by threat actors
- 52% experienced data breaches
- 18% had incidents in the past year
Despite this:
- Average security rating: 83.9 (B)
vs ecosystem average: 90.27 (A) - Ransomware susceptibility (RSI): 0.465 vs 0.378
“Supply chains don’t break at the weakest link.
They break at the most connected one.”
Real-World Example
The CLOP ransomware group exploited widely deployed platforms like:
- Oracle E-Business Suite
- Cleo Harmony
This is not opportunistic hacking—it’s a scalable business model targeting concentration risk.
Pressure Zones: Industries Facing Compound Risk
Manufacturing — Highest Risk Zone
- High ransomware susceptibility (RSI)
- Limited patching flexibility due to operational constraints
Organizations with RSI > 0.8 are 96× more likely to suffer ransomware attacks than those below 0.2.
Healthcare & Education — Largest Downstream Impact
- Healthcare: 254 impacted organizations
- Education: 148 impacted organizations
These sectors combine:
- High data sensitivity
- Complex supply chain dependencies
→ Result: uncontrollable cascading impact
Identity Attacks: The Universal Weapon
Groups like Scattered Spider shifted tactics:
- Phishing
- Vishing
- MFA fatigue attacks
- SIM swapping
- Helpdesk impersonation
When vendor credentials are already exposed, trust-based security boundaries collapse entirely.
5 Immediate Actions for CISOs
1. Identify Your “Critical Weak Core”
Map concentration risk—not just vendor lists.
Focus on shared platforms that can trigger cascading failure.
2. Move from Static Assessments to Continuous Intelligence
Replace questionnaires with real-time monitoring:
- Infostealer exposure
- Active targeting signals
- CISA KEV updates
3. Prioritize Pressure-Zone Vendors
A vendor with an “A” rating may still be high-risk if:
- KEV vulnerabilities remain unpatched
- RSI is high
4. Demand Identity Security Transparency
Assess:
- MFA reset procedures
- Helpdesk verification protocols
- Privileged access control
5. Assume Breach—and Build Resilience
Plan for failure of critical vendors (e.g., Salesforce, MFT platforms).
Quantify:
- Financial impact
- Operational disruption
Invest in redundancy and incident response readiness.
Data Scope & Methodology
- Timeframe: Jan 1 – Dec 31, 2025
- Methodology: Multi-source intelligence analysis including:
- Verified disclosures
- Black Kite platform telemetry
- Supply chain relationship data
Frequently Asked
When multiple organizations rely on the same vendors, a single breach can trigger widespread cascading impact.
Investigation complexity, Legal concerns, Reputation risk, Weak regulatory requirements. Even when breaches are detected in 10 days (median), disclosure still takes 73 days (median).
It identifies vulnerabilities actively exploited in the wild. 70% of top vendors have at least one KEV-listed vulnerability.
A composite metric measuring ransomware risk based on: Patch management, Email security, Identity exposure, Operational weaknesses.
Ready to enhance your cybersecurity strategy?
Transform your organization’s cybersecurity approach into a competitive edge. Schedule a consultation with us today to explore tailored solutions that meet your needs. Don’t wait—empower your security posture now.
Products
About Us
Resources
Receive Our Newsletter
© 2026 ACE PACIFIC GROUP

